What is Shadow IT and how to overcome it
João Simões de Abreu, February 16, 2022
Information systems in large organizations are often a source of frustration for employees. To surpass the limitation of the bulky and outdated systems, teams may build or buy their own IT resources to fulfill their needs or urgent requirements.
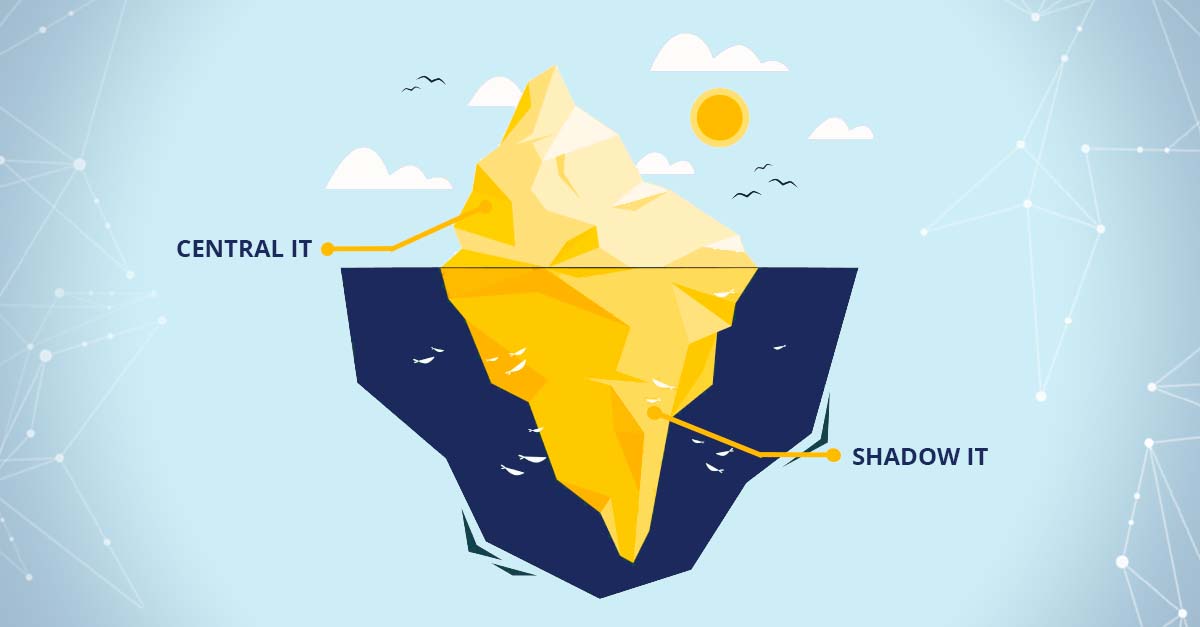
That is Shadow IT: systems developed or acquired by teams outside the central IT department to overcome the flaws of central information systems in order to achieve the required levels of business agility and productivity.
In most organizations, shadow systems’ predominance results in a fragmented application landscape. Consistency, governability, and security are most of the time sacrificed in the process to work more efficiently.
Named systems are frequently more predominant in large organizations. As they grow and evolve, so do their departments’ needs. However, the list of tools made available by central IT does not grow in tandem.
Although it may seem like a lack of effort from the IT department from a business person’s perspective, it is not that IT directors are lazy. On the contrary, as soon as operations grow, so does the complexity of the software, hardware, and networks. Henceforth, the IT department becomes too busy assuring systems are up and running, and people start deviating from their best practices to get the job done.
According to an RSA Data Security Study (The Confessions Survey: Office Workers Reveal Everyday Behaviour That Places Sensitive Information at Risk), although most of the surveyed say they get to have the training about the importance of following security best practices, more than a third of employees say they deviate from the company’s security policies just to get their job done.
Shadow IT systems are born from a good place: the willingness to be more efficient. But they undermine one of IT’s most important aspects: controlling the risks associated with technology in the organization.
Examples of shadow IT applications
- Excel Macros
- Business Intelligence Tools
- MS Access
- Documents stored in a personal cloud storage
- Third-party Software-as-a-Service
Challenges of using Shadow IT applications
Without a good vision of what applications are used in the organization, these solutions can represent risks otherwise mitigated in a controlled environment. Some of the implications of Shadow IT are:
- Security risk – IT cannot assure cybersecurity with the applications deployed outside their supervision;
- Noncompliance – not all tools guarantee departments are complying with laws and regulations, such as the General Data Protection Regulation;
- Data loss or leaks – since IT does not supervise these applications, backup procedures are not provided nor audited. Moreover, when shadow systems’ users depart from the organization, there is the possibility of leaving with proprietary data or leaving behind complicated systems that other team members cannot operate;
- Inconsistent business logic or data – when deploying applications without the IT’s knowledge, business logic may be inconsistent with central guidelines. Likewise, these solutions’ data may be used without an in-depth understanding of the underlying data models. In the worst case, this can result in flawed decisions that may undermine the business;
- Wasted resources – if departments are using shadow IT systems instead of the applications IT consented to do the same job, it may prevent the intended Return on Investment;
- Hidden costs – although shadow applications are most of the time used to surpass the time-consuming central systems, non-IT workers can spend a significant amount of time discussing and re-checking the validity of the data they are using (making the use of the shadow apps redundant).
How to overcome Shadow IT
To surpass the shadow IT barriers, the apparent answer would be “employ more IT experts and educate your people”. However, most organizations do not have the means to hire more people. The answer should be deploying a tool authorized by central IT that is used to quickly build applications that suit every business need – i.e., low-code and/or modeling tools.
By sanctioning a low-code or modeling solution, employees who were already using their ingenuity to build Excel macros and management systems outside central IT will now build secure and reliable applications that do not put businesses at risk.
Although it may seem farfetched to ask for business people to develop their own applications, recent studies point out that, by 2024, eight out of ten technology services and products will be built by people outside IT.
Empowering the workforce with the ability to develop their own solutions is a great way of getting ahead in the digital race. No one understands a given business better than the people running it. Whether from the top hierarchy or the bottom, everyone has different needs that are not met and can be mitigated with the proper software.
By giving ingenious people the power to develop their own applications, organizations can quickly get their ROI back by not depending on so many external software providers and drastically decreasing the risk of non-compliance and data loss.
For instance, Quidgest’s Genio helps organizations with a modeling solution that has several essential features to meet today’s complex business environment:
- Easy to use – a 40-hour course enables people to start deploying small to medium-sized applications;
- Swift – developing solutions is 100 times faster than manual coding and nearly eight times faster than the common low-code platforms;
- Composable – different business capabilities can be grouped, turned on and off, or built on top of a system;
- Continuous evolution – hanging the existing software quickly without breaking it.